What Are You Protecting?
Expand to see our recommendations!
Data - Photos, Documents, Videos

Data can be lost in a few different ways - malware can encrypt it, a bad hard drive can die and lost your data, a computer can corrupt your data. The risks are pretty straightforward though: you would like to protect this data from harm. Here are some solutions we recommend:
- Backups - Backups should be to an external hard drive or NAS (Network-Attached Storage), with access rules to ensure ransomware cannot be spread. Cloud storage is a great option, especially for mobile devices, because it saves space on the device and there are build-in malware protections with most.
Devices - Computers, Phones, Tablets, Servers

Devices are how we access the digital stuff, which is awesome until it isn't working. Here's some ways we recommend protecting your devices:
- Device Protection - Antivirus isn't all you need anymore, especially as more of our lives exist in the digital space. Make sure you have good device protection software installed to protect against 0-day malware and ransomware. If you can't install device protection because of it's age, you should have some other protection on your network (see below).
- Network Protection - If you are unable to install device protection (there are a lot of reasons, but the main one is that there's not a lot of great options or a device is too old), then you need to be protecting your network. Hardware solutions (Firewalls, managed Network Access) are more successful at protecting devices than software protections (VPN), but they can also be difficult to implement.
- Backups - As with data, backups provide a reboot option if a device has a hardware failure. Unfortunately, hardware will sometimes break, and having a backup of your device will ensure you can recover quickly and without loss of information or programs.
ONLINE INTERACTIONS - EMAIL, WEBSITES, CLOUD APPLICATIONS

Online Interactions make up most of our activity when interacting with devices, and the risks vary based on activity. We've broken down suggestions based on the type of interaction - enjoy!
Email:
1. Turn off automatic downloads - Email providers will download a preview of web addresses sent to you if enabled (some do this by default), and this can allow malware to download without ever having to be interacted with by the user.
2. Do not open links - Once automatic downloads is disabled, be sure not to open any of those links. If you are told to visit a website, open a new browser window and enter the website address yourself. Some website addresses can look legitimate, but simple misspellings give the hackers the ability to create a spoofed website that looks legitimate but will only send them your credentials, not send them to your account provider.
3. Spam Protection - If your email provider has spam protection, ensure it is enabled. Most companies pay for more advances spam protections, which can provide encryption and advanced malware protections. If you have a custom domain and an email address that you use for a business, having spam protection software can help relieve some of the spam you experience and keep your business emails more secure.
Websites:
1. Ensure that the websites you visit have a valid certificate - this will help ensure you are communicating with the correct server.
2. User Browser extensions that help keep your traffic encrypted and secure - there are several free browser extensions that can help keep your web traffic more secure. We recommend Ad Blockers, HTTPSEverywhere, PrivacyBadger, and Password Manager extensions to help make your online experience more enjoyable and secure.
Online Applications:
1. Make sure you are interacting with the applications through a secure connection, especially if you are entering personal information or conducting purchases.
SENSITIVE INFORMATION - MEDICAL INFORMATION, CREDIT CARD NUMBERS, ACCOUNTING INFORMATION

If you are interacting with sensitive information, there are a number of regulations you are required to follow (as a business), but even if you are interacting with just your information, there are some best practices for sharing and keeping.
1. Only send sensitive information via an ENCRYPTED or SECURE connection - do not send this information via email unless you know it is encrypted and going to the correct person.
2. Only share information that you absolutely need to. It is incredibly difficult to recover after identity theft, and keeping your information safe involves only sharing as necessary. There are a number of scams targeting personal information (hiring scams, survey scams, dating scams, etc), so double check before sending information.
3. Have some sort of credit monitoring service, or freeze your credit when not using. This can help protect you from identity theft and give you a heads up if you information has been compromised.
Who We Are
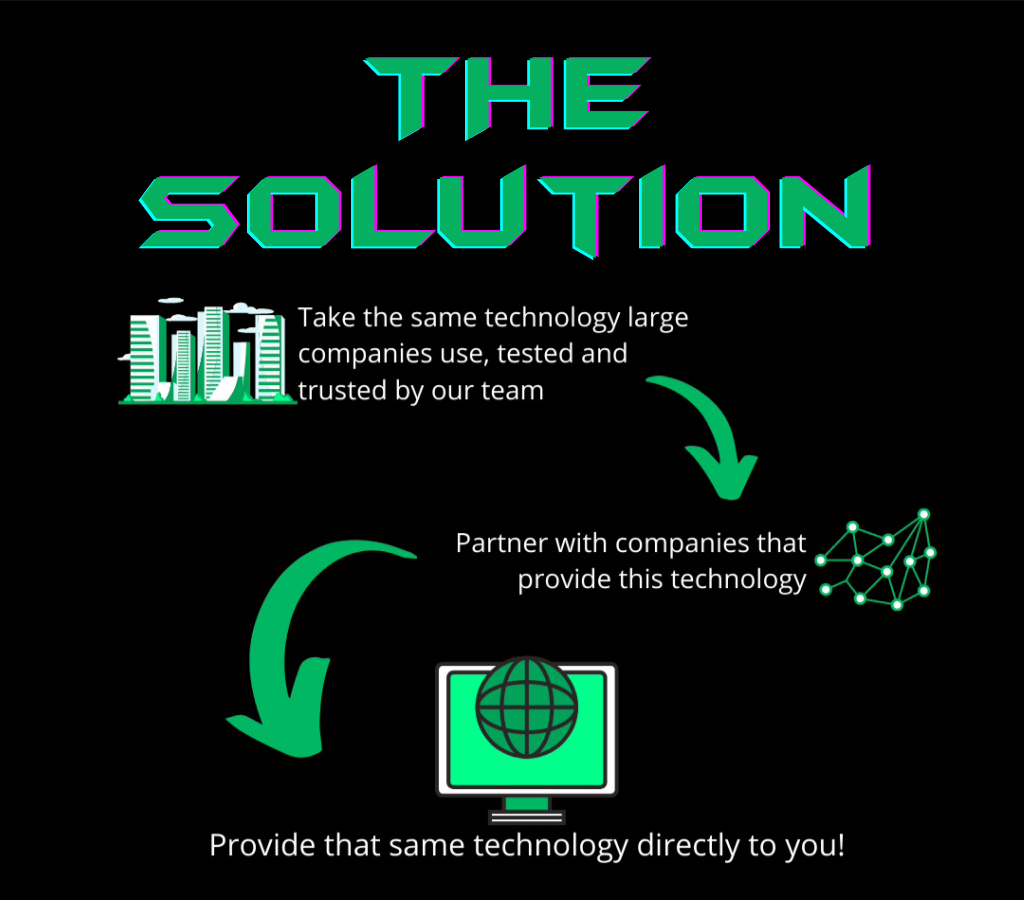
Scion Solutions LLC was founded due to a lack of reliable ransomware protection for home users and micro businesses. We have worked to protect large corporations, but were never able to provide a great answer to the question, “What do you recommend for computer protection?”